AUTOSCAN SYSTEM
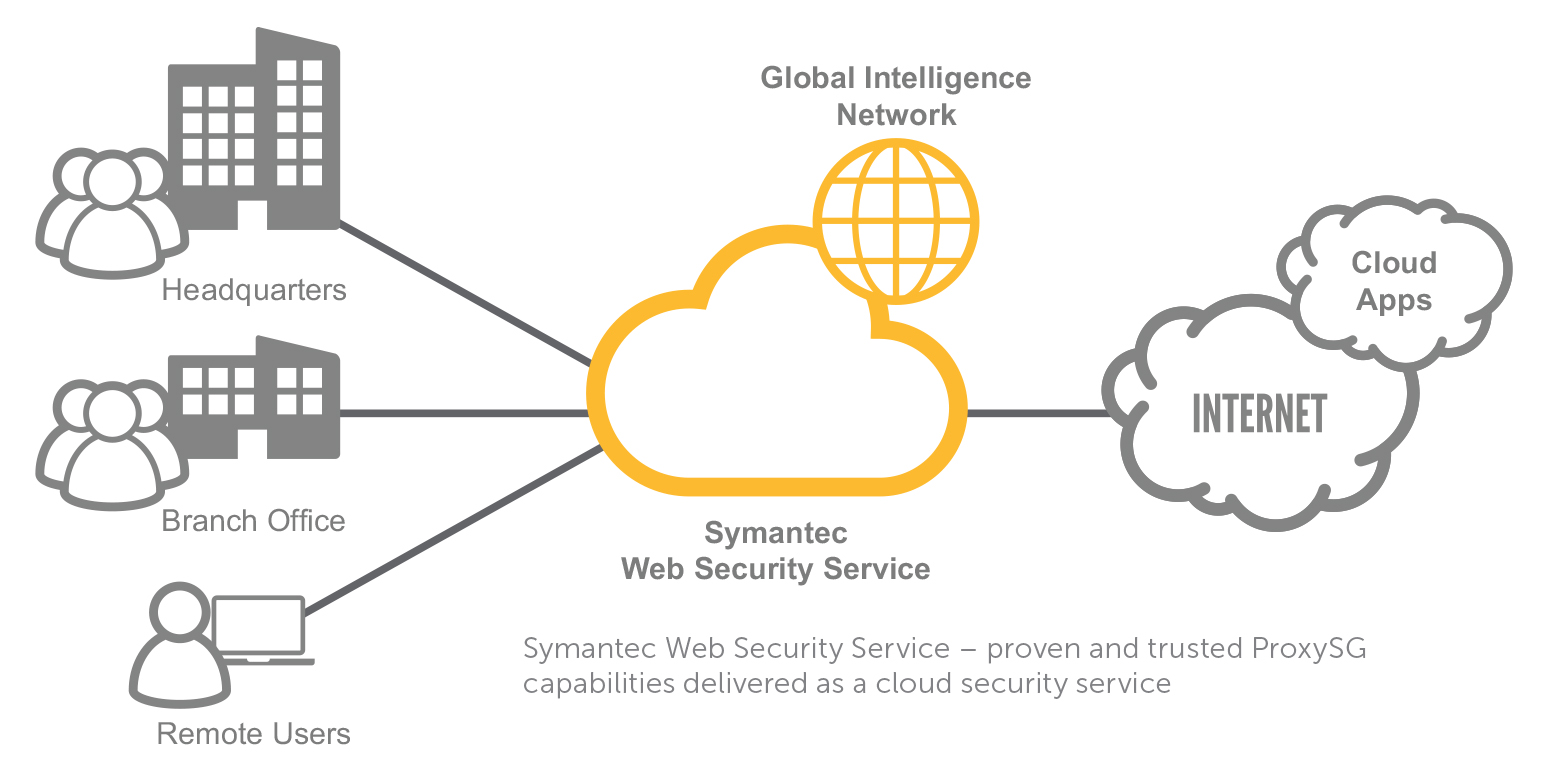
- The system is designed and built to automatically scan for information security vulnerabilities. related to website, IT infrastructure on a large scale space a country’s network (Cyberspace); allows for custom configuration to serve scanning missions in other countries as required.
- The system allows integration with other information security monitoring systems to provide an overall picture and timely warnings of threats on a national cyber scale.
- The system allows managers to build response plans to protect national sovereignty on Cyberspace when attacked by cyber attacks through analysis of collected risk data.
- The system is supplemented with diverse data sources, as well as regularly updated with the latest vulnerability data, analyzing trends and common threats on Cyberspace.
- The system enables effective support for in-depth analysis, remediation and vulnerability exploitation through an artificial intelligence technology platform, as well as a smartly designed management platform that allows for automatic scheduling, monitoring and reporting.
- The system allows building reports according to different scenarios, as well as customization according to user requirements.
- Sysstem included bellow product have already sale to Ip-Tribe Singapore, Emirates, Lotus Cargo, SoftBank, TPC Technology, Singtel, M1, Singapore Government, VNPT group, AT&T, UAE Gov
- WSS-WEB: Wide Scanning software for WEB:
- (1) Vulnerability detection according to OWASP Top 10 & CWE Top 25, large vulnerability database.
- (2) Allows combining with target data sources from scanning systems such as: Shodan, DNS Lookup…
- (3) Automatically identify and list important website information on Cyberspace.
- (4) Self dynamic release present, collect decade information about operating system, programming language, system CMS content management and web server configuration; automatic URL extraction and website structure vulnerabilities.
- (5) Data security testing: Identify weak passwords, leaked information leak, configuration error …
- (6) Collect numbers quantity big target information on the lips Internet
- (7) Yes ability power sweep rule tissue big up to 1,000 websites at the same time (Optimizes the 10Gbps bandwidth to load and analyze data from 100,000 – 200,000 websites within 24 hours with ~280.000 CVEs; guaranteed accuracy > 90%)
- DSS-WEB: Deep scanning software for WEB:
- (1) Automatically collect detailed information about the web server, including operating system, software version, and security configuration.
- (2) Identify programming languages such as PHP, Java, .NET, JavaScript and website support technologies.
- 3) Determine website development platform like WordPress, Joomla, Drupal, CakePHP, SharePoint.
- (4) Analysis of the ports and services running on the server, helping to assess exposure.
- (5) Confirm determine website structure by scanning and listing all URLs, including hidden ones, for detailed
- (6) Automate periodic inspection schedules through automatic security scan scheduling to ensure systems are always monitored and protected.
- (7) Enables intelligent scanning to quickly and accurately identify vulnerability types through analysis of data collected from the target.
- (8) Enables website system testing: Provides the ability to scan and analyze web applications to identify common vulnerabilities, including XSS (Cross-Site Scripting), SQL Injection, CSRF (Cross-Site Request Forgery) and other security risks.
- WSS-NET: Wide scanning software for NET:
- (1) Comprehensive scan of network components, automatically identify devices on the range IPv4 and IPv6 addresses.
- (2) Detect security weaknesses such as Weak Authentication; Unpatched Firmware; Insecure Communication.
- (3) Service and operating system analysis: x identify services running via TCP/UDP protocols; identify operating system, version, and detailed configuration.
- (4) Metadata analysis Device: stores metadata, analyzes trends, extracts information about new vulnerabilities recorded over time and for each device category.
- (5) History use the direction France smart to overcome the system wall fire, IDS/IPS or the muscle regime tell guard different, sure tell next near dark Multi the item pepper in network.
- (6) Collect large amounts of target information on network infrastructure.
- (7) Capable of large-scale scanning of up to millions of devices, processes 5.000 – 10.000 network devices concurrently (1,000,000 network devices in 24 hours with ~280.000 CVEs, ensuring accuracy > 90%).
- DSS-NET: Deep scanning software for NET
- (1) Detect and warn of security vulnerabilities and weaknesses throughout the network system.
- (2) Detailed warnings for each organization.
- (3) Identify abnormalities such as changes in the number of devices, ports, or services on the network.
- (4) Instant alerts of vulnerabilities/exploitation risks via Email, SMS or Slack.
- (5) Detect all devices in the network, including servers, computers, printers, cameras, and IoT devices.
- (6) Collecting information on infrastructure layers: ports, services, software versions, and operating systems.
- (7) Detect vulnerabilities/weaknesses on multiple platforms such as Windows, macOS, Linux, Solaris, Cisco, and database management systems (Oracle, MySQL, PostgreSQL, MongoDB…).
- (8) Enables intelligent scanning to quickly and accurately identify vulnerability types through analysis of data collected from the target.
- (9) Display vulnerability details according to CVE, CPE and OVAL security standards; classified into 4 levels: Severe, High, Medium and Low.
- iStealther: Anonymous Software
- (1) Create independent IP from fixed network and SIM with Internet, with unlimited scalability according to hardware resources.
- (2) Multi- support form Proxy types such as static, rotating and private.
- (3) Integrate SIM to utilize IP from mobile network, increase anonymity and geographical diversity from many countries, depending on the geographical location of VPS server.
- (4) Supports HTTP, HTTPS, SOCKS5 protocols and optional Tor onion routing to meet the needs of darknet access or advanced applications.
- (5) No gender limit number time replace reset /change IP for rotating proxy, make sure tell calculate sacred active in too program history Use; automatic detection and replacement mechanism for IPs blacklisted by major platforms (Facebook, Twitter, Instagram, etc.).
- DMS: Scanning Distribution Software
- (1) Allows flexible management of target list, setting target priority, and labeling targets.
- (2) Manage scan status.
- (3) Perform classification, sorting and target division for scanning software.
- (4) Optimal scanning object division Guaranteed completion within the desired time frame.
- (5) Provide a solution to avoid activating defense systems when performing mass scans on targets.
- (6) Ability to perform scans with NO limit on targets. With a large set of input targets, the scan engine can be calculated and expanded to speed up execution, reducing total scan time.
- iKingtest: Vulerability testing software
- (1) Providing multi-platform vulnerability testing solutions form script, background popular.
- (2) Provide a solution to share test payloads between units.
- (3) Provide complete information after the testing process such as: response time, success/failure rate, or errors encountered.
- (4) Allows integration of information from other testing tools such as Selenium, JMeter or testing frameworks to provide comprehensive reporting.
- iManager: Centralized management software
- (1) Processing requests scan bridge; Total fit newspaper report; Scan core management; Management user management; Analysis right access update sign active dynamic; copper set muscle office data Information Security; Support support fake set payload of scan command and find set Reference number dark advantage; for permission Build reports for different scenarios, as well as customize them according to user requirements.
- (2 ) Scene newspaper time space real give permission to send information newspaper right When release presently hole gap serious important via email, Slack , Teams, Tele or the system system scene newspaper other ; support support product fit with webhook to click active onion dynamic on one’s own dynamic based on above conclude fruit scan
- (3) Integration with other monitoring systems: Automatically send scan results and vulnerability-related data (CVE, severity) to SIEM systems such as Splunk, ArcSight, QRadar, or Elastic Stack; Export data in popular log formats such as JSON, CEF (Common Event Format), or LEEF (Log Event Extended Format) for easy integration.
- DBSC: Bigdata Storage and Collection software
- (1) Collect from Multi Data source type: new vulnerability emerges collected from CVE, NVD… databases; Exploits collect decade from exploit code repositories such as Exploit-DB, GitHub Security Advisories; n Threat Intelligence sources connected to platforms such as MISP (Malware Information Sharing Platform), ThreatConnect; automatically collects information from famous security forums such as Hack Forums, Bug Bounty Platforms…
- (2) Allows flexible configuration through definition meaning before Targeted collection tasks (e.g., product-, technology-, or industry-specific vulnerabilities); specify collection sources such as RSS feeds, APIs, or websites.
- (3) Supply grant prize France copper set data whether from Internet in network private.
- (4) Collection is performed in parallel to optimize performance.
- (5) Processing and storing raw data and classifying data on the source above background block labour turmeric data whether Big data
- ACSLT: Automatic Cyber Security Language Translator
- (1) Multi Language translation conclude scan result, solution France fix …, allow easy search.
- (2) Depending select newspaper fox equal Multi language Older brother.
- (3) Search sword conclude bilingual fruit
- iCSC: Intelligent Cyber security chatbot
- (1) Interact with users by voice; convert text to speech.
- (2) Smart search on the system’s information security database.
- (3) Synthesize and create automatic reports (synthesis from scanning data sources, analysis of information security loss trends…, recommendations).
- (4) Allows for vulnerability analysis and provides guidance to assist in vulnerability remediation.
- (5) Allows generating basic exploit codes based on vulnerabilities, allowing users to customize as required.
- (6) Automatically check the validity of the mining code entered by the user.
- ASR-Cyber: Automatic Speed Recognition for Cyber language
- (1) Search target.
- (2) Scan command target.
- (3) Search conclude scan result, item pepper Satisfied scan
- (4) Support support read newspaper fox total fit conclude fruit scan
- (5) Choose select tone speak edema fit read report.
- (6) Depending adjust speed reading




Reviews
There are no reviews yet.